The quantum computing threat to blockchain security has always carried an asterisk: eventually. A problem for future engineers, future regulators, future protocol developers. Google’s latest research just yanked that asterisk out of the sentence.
Researchers at Google have published findings suggesting that breaking ECC-256 — the elliptic curve cryptography standard that protects the vast majority of altcoin wallets — may require fewer than 500,000 physical qubits. That’s roughly 20 times fewer than previous estimates had indicated. The timeline compression this implies isn’t academic. It’s the kind of number that should be forcing emergency agenda items at every serious altcoin security committee on the planet.
The Number That Changes Everything
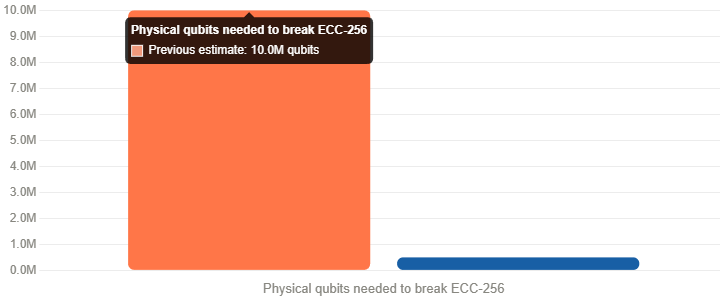
Prior estimates placed the qubit requirement for cracking ECC-256 in the range of 10 million physical qubits — a figure so large it conveniently pushed the threat horizon well past anyone’s realistic planning window. Google’s revised figure of sub-500,000 qubits doesn’t just bring that horizon closer. It puts it squarely within the trajectory of machines that are being actively built right now.
To put this in context: IBM’s Heron r2 processor currently operates at 156 qubits. Google’s own Willow chip hit 105 qubits in late 2024. The gap between today’s machines and the 500,000-qubit threshold is still enormous — but it’s no longer the kind of gap that lets you defer the problem indefinitely. Qubit counts have been scaling rapidly, and error correction research — the other major bottleneck — is advancing in parallel.
The year 2029 has started appearing in researcher conversations as a plausible, if aggressive, window. That’s not a guarantee. It’s a warning shot.
Nine to Twelve Minutes to Crack a Bitcoin Wallet
The attack scenario Google’s researchers describe is what makes this finding genuinely alarming rather than merely technically interesting. Their calculations suggest a successful ECC-256 break could be executed in 9 to 12 minutes with a sufficiently capable quantum machine.
For anyone familiar with how Bitcoin works, that window is immediately recognizable: it’s roughly the time required to produce one Bitcoin block. The implication is that a quantum attacker wouldn’t need sustained, hours-long compute time to compromise a target wallet. They’d need a window shorter than a single block confirmation. That timeframe is operationally realistic in ways that previous multi-hour attack scenarios simply weren’t.
The attack vector here is specific. ECC-256 protects the relationship between a Bitcoin wallet’s public key and its private key. When you broadcast a transaction, your public key becomes visible on-chain — and it’s during that brief exposed window that a quantum computer running Shor’s algorithm could theoretically reverse-engineer your private key. In a sub-10-minute attack scenario, the exposure window aligns uncomfortably well with normal transaction processing time.
Which Wallets Are Actually at Risk
Not every Bitcoin holder faces equal exposure, and understanding the distinction matters.
The most immediately vulnerable addresses are those with exposed public keys — primarily wallets that have already sent a transaction (making the public key permanently visible on-chain) and, critically, old pay-to-public-key (P2PK) format addresses used in Bitcoin’s early years, including wallets attributed to Satoshi Nakamoto. These addresses don’t benefit from the additional hashing layer that modern P2PKH addresses use, meaning the public key is already sitting in plain sight on the blockchain, permanently.
Then there are the inactive wallets — millions of BTC sitting in addresses that haven’t moved in years, some likely lost, some intentionally held long-term. Many of these use older address formats. If quantum capability reaches the threshold Google’s researchers describe, these become high-value targets: known balances, exposed keys, no active owner monitoring the address for suspicious activity.
The cumulative Bitcoin at risk across these categories runs into the millions of BTC. Even a fraction of that being compromised would constitute one of the largest wealth-transfer events in financial history — and it would detonate confidence in the entire altcoin ecosystem at a structural level.
Post-Quantum Cryptography: The Clock Is Ticking
Google isn’t just raising the alarm without pointing toward a solution. Their researchers are explicitly urging the industry to accelerate the shift to post-quantum cryptographic standards — and the urgency in that message reflects how long these transitions actually take in practice.
The US National Institute of Standards and Technology (NIST) finalized its first set of post-quantum cryptographic standards in 2024, including CRYSTALS-Kyber for key encapsulation and CRYSTALS-Dilithium for digital signatures. These algorithms are designed to resist quantum attacks — but deploying them across existing blockchain infrastructure is not a flip-a-switch operation. It requires protocol upgrades, wallet software changes, node operator coordination, and community consensus processes that historically take years to complete.
Bitcoin’s development culture is deliberately conservative. Changes to core cryptographic assumptions require overwhelming consensus, extensive testing, and careful backwards-compatibility engineering. The same is true across most major altcoin networks. Which means the migration window needs to open now — not when the first quantum machine capable of executing the attack is switched on.
The altcoin ecosystem has navigated technical upgrades before. SegWit took years of contentious debate. The Ethereum merge from proof-of-work to proof-of-stake was in development for over five years before execution. Post-quantum migration makes both of those look simple by comparison.
Why This Matters Beyond Bitcoin
The implications extend well past Bitcoin’s balance sheet. ECC-256 and its close relatives are the cryptographic backbone of essentially the entire altcoin ecosystem — Ethereum, Solana, Layer 2 networks, DeFi protocols, cross-chain bridges. A viable quantum attack on elliptic curve cryptography doesn’t threaten one chain. It threatens the foundational assumption that private keys are private.
The altcoin space has built a multi-trillion-dollar ecosystem on the premise that reversing a public key to its private key is computationally infeasible. Google’s researchers are saying that premise has a more visible expiry date than previously believed.
For developers, this is a call to start integrating post-quantum signature schemes into roadmaps immediately. For protocol governance bodies, it’s a case for fast-tracking research into quantum-resistant upgrade paths. For holders with significant long-term positions in old-format addresses, it may be time to migrate funds to addresses that benefit from modern hashing protections — before the option to do so quietly, without urgency, quietly disappears.
2029 may or may not be the year a quantum computer breaks ECC-256. But the window for comfortable, unhurried preparation is narrowing fast — and Google just made sure the industry knows it.
Leave a Reply